Is Your Business a Hacker's Easy Target?

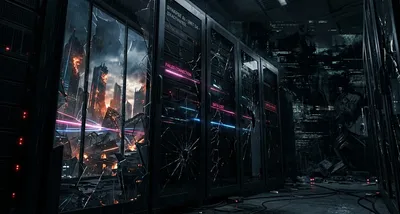
Imagine this: You run a small online bakery. Orders are flowing, customers are happy, and your website handles payments smoothly—until one morning, you can’t log in. A message pops up: “Your files are encrypted. Pay $5,000 to get them back.” Your customer data, order history, and even your website are locked. No sales. No access. Just panic.
This isn’t a hypothetical scenario. It’s happening to small businesses every day. Hackers don’t just go after big corporations—they target easier prey. And if you think your business is too small to be on their radar, think again.
Is Your Business at Risk? Why Hackers Love Small Targets
You might assume cybercriminals only chase high-profile companies with deep pockets. But here’s the truth: small businesses are often more vulnerable—and hackers know it.
Why? Because many small business owners don’t prioritize cybersecurity. They might use weak passwords, skip software updates, or assume their basic antivirus is enough. That makes them low-hanging fruit for attackers. A recent study found that 43% of cyberattacks target small businesses, and 60% of those attacked go out of business within six months.
Think about your own business:
- Do you store customer data (names, emails, payment details)?
- Do you rely on a website or online payments?
- Do you use cloud tools (like email, invoicing, or file storage)?
If you answered yes to any of these, you’re a potential target.
What Is ‘Pentesting’—and Why Should You Care?
So, how do you find your weak spots before a hacker does? That’s where penetration testing—or “pentesting” for short—comes in.
Pentesting is like a security fire drill for your digital systems. You hire ethical hackers (the “good guys”) to simulate a real cyberattack on your website, network, or software. They try to break in—just like a criminal would—but instead of stealing your data, they report back with a list of vulnerabilities.
Think of it this way:
- Traditional security is like locking your doors and windows.
- Pentesting is like hiring a burglar to test if those locks actually work.
It’s not about scaring you—it’s about giving you actionable insights to fix problems before they become disasters.
The Real Cost of a Breach: It’s More Than Just Money
A cyberattack isn’t just an inconvenience. It can cripple your business in ways you might not expect. Here’s what’s really at stake:
1. Data Loss = Lost Trust
If customer data (like credit card numbers or personal details) is stolen, you could face legal trouble, fines, and a PR nightmare. Customers won’t trust you with their information again—and rebuilding that trust takes years.
Example: A small dental clinic in Amsterdam suffered a data breach last year. Patient records were leaked, leading to lawsuits, lost clients, and a damaged reputation. The clinic spent months recovering—and some patients never came back.
2. Downtime = Lost Revenue
If your website or payment system goes down, you can’t take orders, process sales, or serve customers. For a small business, even a few hours of downtime can mean thousands in lost revenue.
Example: A popular Rotterdam restaurant’s online ordering system was hacked. For three days, they couldn’t take reservations or deliveries. They lost €12,000 in sales—and some regulars switched to competitors.
3. Ransomware = Extortion
Some hackers don’t just steal data—they lock you out of your own systems and demand payment to restore access. Paying the ransom doesn’t guarantee you’ll get your data back, and it funds more attacks.
Example: A freelance graphic designer had all her client files encrypted. She paid the €3,000 ransom—only to find the hackers demanded another €2,000 a week later.
4. Reputation Damage = Long-Term Pain
Once word gets out that your business was hacked, customers may take their business elsewhere. Rebuilding your reputation can take years—if it’s even possible.
Example: A small e-commerce store selling handmade jewelry lost customer data in a breach. Within months, their sales dropped by 40% as shoppers switched to competitors they trusted more.
Pentesting Gets Smarter: AI is Changing the Game
Traditionally, pentesting was expensive, slow, and complicated—something only big companies could afford. But that’s changing.
New tools are making pentesting faster, cheaper, and more accessible for small businesses. One of the biggest shifts? Artificial Intelligence (AI).
Here’s how AI is making pentesting better:
- Faster scans: AI can analyze your systems in hours instead of days.
- Smarter prioritization: It flags the most critical vulnerabilities first—so you know what to fix immediately.
- Clearer reports: Instead of technical jargon, you get plain-language explanations of risks and how to fix them.
Companies like NetSPI are leading this shift. Their new platform is designed to be simple enough for non-technical business owners—with features like:
- “Two-click” fixes for common security gaps.
- Automated reports that explain risks in everyday language.
- AI-powered recommendations on how to improve security.
As one security expert put it:
“We designed the NetSPI experience around how security teams actually work. Pentesting should help you answer critical questions quickly, prioritize what matters, and move straight from insight to action—with clarity and confidence.”
This means even a small business owner—without a dedicated IT team—can now identify and fix security gaps before hackers exploit them.
What You Can Do Today to Protect Your Business
You don’t need to be a tech expert to improve your security. Here are five simple steps to get started:
1. Start with the basics
- Use strong, unique passwords (and a password manager like Bitwarden or 1Password).
- Enable two-factor authentication (2FA)—an extra security step, like a code sent to your phone.
- Keep your software and devices updated (hackers exploit old, unpatched systems).
2. Get a security check-up
- Run a free vulnerability scan (tools like Nessus Essentials or OpenVAS can help).
- If you handle sensitive data (like payments or customer info), consider a professional pentest.
3. Train your team
- Teach employees how to spot phishing emails (fake messages designed to trick them into revealing passwords).
- Set clear security policies (e.g., “Never share passwords over email”).
4. Backup your data
- Use automated cloud backups (like Backblaze or Google Drive) so you can restore files if attacked.
- Store backups offline (so hackers can’t encrypt them too).
5. Talk to a security expert
- If you’re unsure where to start, consult a cybersecurity professional. Many offer affordable security audits for small businesses.
FAQ: Your Pentesting Questions Answered
”Isn’t pentesting only for big companies?”
No! Small businesses are actually more likely to be targeted because hackers assume they have weaker security. Pentesting helps you find and fix vulnerabilities before criminals do—regardless of your size.
”How often should I get a pentest?”
At least once a year, or whenever you:
- Launch a new website or app.
- Make major changes to your systems.
- Handle sensitive customer data (like payments or medical records).
”What’s the difference between a pentest and a security scan?”
- A security scan is like a quick health check—it flags potential issues but doesn’t test them.
- A pentest is like a full stress test—it actively tries to break in to find real weaknesses.
IT Move NL
Whether you run a webshop, a dental clinic, or a local café, cybersecurity isn’t just an IT problem—it’s a business survival issue. The good news? You don’t need to be a tech expert to protect yourself. Tools like pentesting are becoming faster, smarter, and more accessible—so even small businesses can stay ahead of threats.
If you’re not sure where to start, we’re here to help. Let’s talk about what makes sense for your business—no jargon, no pressure. Just practical advice to keep your data (and your customers) safe.
Sources:

He/Him · AWS Certified Solutions Architect | Cloud Engineer @ Essent
Cloud Engineer at Essent B.V. with 10+ years of experience in the tech industry. AWS Certified, passionate about serverless architectures, Infrastructure as Code, and DevOps. Proficient in TypeScript, Python, and Terraform. Based in Amersfoort, Netherlands.
STAY IN THE LOOP
// Cloud, AI & DevOps insights — straight to your inbox.
No spam. Unsubscribe anytime.
// Related articles
Need help with your cloud infrastructure?
Our team of experts is ready to help you navigate the complexities of modern cloud architecture.
Get in Touch